GLOSSARY OF SECURITY TERMS
Certificate
Digital document issued by an independent entity that guarantees the identity of systems and people on the internet. The security of the certificate is protected by cryptographic techniques.
Malware
Any programme with an annoying, malicious or illegal intent. They are generally
designed to be executed without the user's intervention.
Password
Set of letters, figures and symbols, or even phrases, used to authenticate users in a computer system. For passwords to be effective, they have to be selected such that they are difficult for an attacker to guess.
Correos encadenados
Son mensajes de correo electrónico en los que se pide que el mensaje sea enviado a más gente para que estas personas también los reenvíen. Es una de las posibles fuentes de problemas con el correo electrónico, ya que a menudo llevan noticias falsas, pueden ser portadores de virus, etc.
Cryptography
Discipline that deals with the security of the transmission and storage of
information.
Worm
Type of malicious code whose main characteristic is that it copies itself from one system to another via the internet.
Denial of service
Computer attack that, while not affecting the information contained in a system, leaves it unable to provide any services. The denial can be achieved by saturating or overloading the servers.
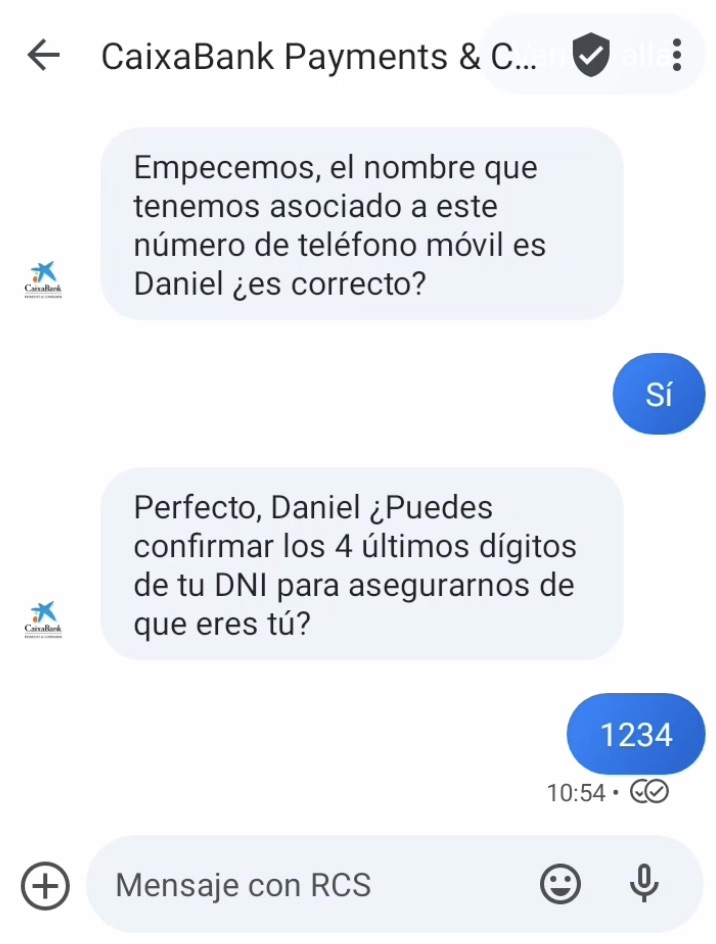
Social Engineering
Techniques that attempt to breach the security of computer systems by deceiving their users and/or administrators. Most social engineering techniques are similar to scams.
Spyware
Spyware programs are malicious or misleading applications that are installed together with other programs that the user downloads. This type of program can execute multiple actions.
Some are used to gather information on the system in which they are installed, which they
send via internet; others constantly display undesired ads or modify the pages viewed to include links that were not in the original. All these actions are masked with confusing authorisations, meaning the user is not usually aware of this.
Content filtering
Set of technologies that allow the information transmitted via the internet to be filtered. Content filtering is used to block viruses sent by email, to control minors' access to the internet, etc.
Cookie
Information sent by an internet server to the web browser that is used later on subsequent connections. They can be used for legitimate purposes, such as to identify users, and for malicious ones, such as the unauthorised storage of browsing habits.
Intrusion
Computer attack in which the attacker manages to get complete control of the computer. During the intrusion, the attacker can access and alter all the data on the computer, modify its operation and even attack other computers.
Spam
Unwanted commercial email sent via the internet. The volume and content of spam can make it considerably more difficult to use email services.
Phishing
Phishing attacks rely on misleading emails and fraudulent servers to trick users of internet services. In the case of financial institutions, the goal is to try to make users disclose their data, such as their credit card number or PIN. More information on Phishing.
Proxy or intermediate server
Computer system whose mission is to act as an intermediary between one system and another through the internet. The roles of a proxy include speeding up internet access, filtering the content accessed and protecting systems by preventing direct communications.
Electronic signature
Digital information associated with a specific transaction carried out online that, together with certificates, is used to identify the participants in the transaction.
Firewall
Computer system that controls which machines and services in a network
can be accessed. It can be a specialised system or an installed program
(personal firewall). When this check involves the information transmitted and not
just on the connection, the system used is a proxy.
Trojan
Malicious code camouflaged inside another program that seems useful and harmless. Trojans can be hidden inside known programs, meaning the software has to come from a reliable source.
Virus
This is the best-known type. It is a program that is copied inside other programs and tries to reproduce itself as many times as possible. Although this is not always the case, most often the virus, in addition to copying itself, alters or destroys the information of the systems where it is run.
Encryption
The encoding of data using various mathematical techniques to ensure
it can be transmitted securely.
EC brochure: on the rights of payment service users pursuant to PSD2